Managed Security Services (MSS)
Explore the latest managed security services for today's hybrid cloud world
Read the 2024 ransomware trend reportMekas Security helps protect enterprises with an integrated portfolio of products and services, infused with security AI and automation capabilities. The portfolio enables organizations to predict threats, protect data as it moves, and respond with speed and precision while allowing for innovation.
As your trusted advisors, Mekas Security™ specialists help you address your security needs, from the simplest to the most complex, monitoring and managing security incidents 24x7x365. Our people, technology, facilities and processes are among the best in the world.
Your organization may have working tools and processes but could benefit from trusted security advisors. Mekas® Managed Security Services can augment your security program with tailored services, including threat management, cloud, infrastructure, data, identity and response management.
Some organizations require help with developing a continuous improvement process to protect their enterprise during multi-year projects. Mekas MSS specialists can help optimize, fine-tune, and improve security program efficiency for the long-term.
Setup a discovery call with our engineers Contact us

Protect critical assets from vulnerabilities, detect advanced threats and quickly respond and recover from disruptions.

Protect, prevent, detect and respond to endpoint threats around the clock, fueled by threat intelligence and proactive threat hunting.
Protect enterprise endpoints in today’s distributed and remote-first environment with antivirus, data loss prevention and encryption.
Applying our deep industry expertise, Mekas Consulting partners with our clients to address each company's unique talent goals and challenges, dig deep to understand their workforce realities and create strategies that unlock new levels of performance inside their business. Together, we reimagine Human Resources with AI at the core—delivering business value, accelerating the digital agenda, unlocking workforce potential with market-relevant skills, and creating an agile HR function—maximizing the human-machine partnership.
Generate better experiences and more predictable outcomes throughout the hiring lifecycle. Use HR data and market metrics to segment audiences and co-create candidate personas for optimal staffing.
Our services combine deep process and technology expertise infused with AI to create innovative workforce operating models across your candidate and employee experience.
Many organizations now seek to outsource parts or all of their cybersecurity functions to a trusted security provider. Managed security services (MSS) is a service model or capability provided by cybersecurity service providers to monitor and manage security devices, systems, and even software-as-a-service (SaaS) applications.
A managed security services provider (MSSP) offers around-the-clock (often 24x7or 8x5 support) information security monitoring and management. A global, proactive protection delivery model helps detect and triage malicious security events.
As organizations scale and compete, protecting endpoints, assets and data from exfiltration, breach or other cybersecurity events becomes paramount. The complexity of the security landscape has changed dramatically over the last several years, and organizations need to stay ahead of a rapidly changing threat landscape.
It can add rare, specialized cybersecurity skills to your team, such as cloud security, identity or compliance knowledge, without the need to build your own expensive security operations center. It can also help prevent breaches through automated incident response, remove complexity in security, reduce alert fatigue for in-house resources, and provide proper compliance governance.
An MSSP like Mekas Security offers security as a service on IT and information security systems: threat monitoring, infrastructure management, availability, capacity management, proactive protection and response capabilities.
A managed services provider (MSP) generally provides only operational support to keep systems and applications at an agreed-upon service level agreement (SLA).
Security information and event management (SIEM) tools, endpoint detection and response solutions and traditional network security tools are just some. Secure access service edge (SASE), cloud access security broker (CASB), container security software, and even cloud-native cybersecurity solutions within AWS, Azure, and GCP can also be part of the engagement.
Modern MSSPs like Mekas can monitor and manage the security within public, multicloud, IaaS provider platforms. This can help your organization improve its visibility and context into the overall security program and reduce risk from misconfigured cloud resources.
Regulatory policies are constantly evolving. A global MSSP like Mekas brings knowledge of regional and industry frameworks and regulatory requirements. The security provider can help assess current state of security and provide real-time visibility into compliance posture.
Managed security clients will usually log in to a secure portal to submit requests. The cybersecurity provider can then change policies, triage security events, send an alert or even automate response to an incident. The client may also use their MSSP’s dashboards to generate reports on security device status, the number of security events and vulnerabilities, SLA activity and more.
MSSPs provide an array of skilled professionals, such as onboarding specialists, security analysts or service delivery experts, engineering and support, project management and customer service. More specialized roles such as incident response, threat intelligence and threat hunting can be added, depending on the desired scope of the engagement.
3031 Tisch Way, 110 Plaza West
San Jose, CA 95128
Level 1, MidTown Building, Road No. 1
Banjara Hills, Hyderabad, Telengana, 500034
+1 844-549-0999
Stay ahead of the latest threats to the security landscape, thought leadership and research
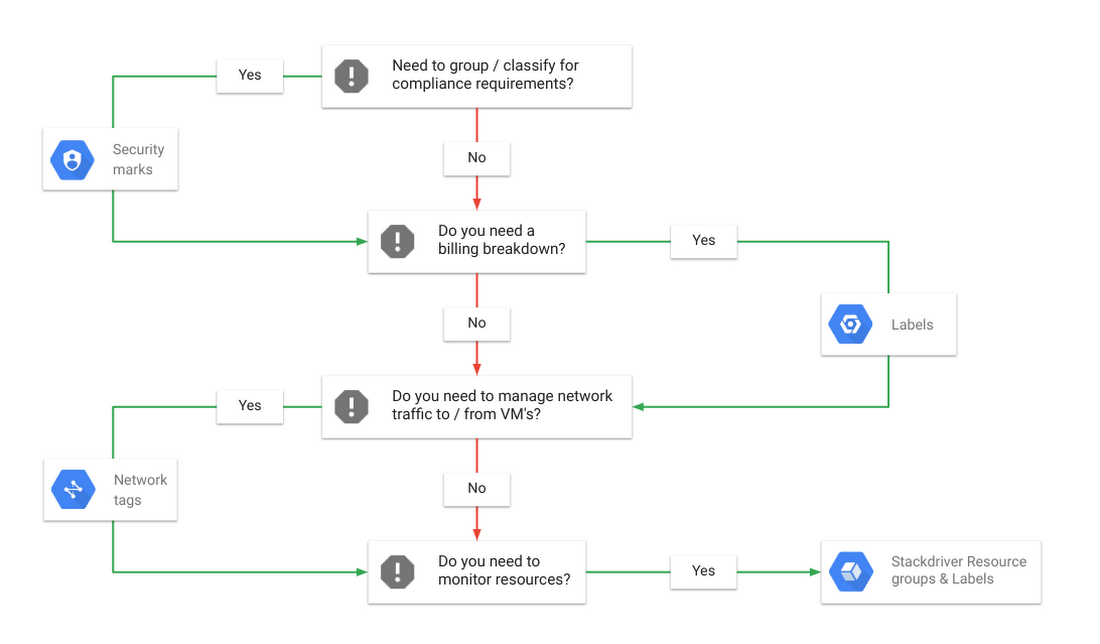
Labeling Google Cloud Platform resources Do you run and manage applications on the Google Cloud Platform (GCP)? Do you need to group and classify your GCP resources to satisfy compliance requirements? Does your finance team is asking for visibility on which team is spending where and how? Do you want to track GCP resource utilization […]
Read More
Authors & Credits: Imperva,Raj Meka Introduction Most mid-sized to large enterprises have already moved some of their infrastructure, data, and workloads into the cloud for better agility, efficiency, and cost savings. Nearly three-quarters of businesses are running a hybrid and/or multi-cloud strategy today, according to Forrester Research. Cloud migrations are often part of larger corporate […]
Read More
Authors & Credits: Ben Hagai Global Migration Practice Lead, Professional Services, Google Cloud Kuntal MitraTechnical Account Manager, Professional Services, Google Cloud Contact us Cloud migration is one of the biggest organizational changes that technologists will go through this decade, with a profound impact on a business’s ability to innovate and its overall economics. Migrating to […]
Read More